UUID Generator – Complete Guide to Generate V1, V3, V4 & V5 UUIDs
Have you ever needed a unique identifier for a database record, an API key, or a file name and wondered how to generate one that is guaranteed to be unique? Or maybe you have seen strings like "550e8400-e29b-41d4-a716-446655440000" in code and wondered what they are?
I remember building my first web application. I needed a way to identify each user in my database. I thought about using auto-incrementing numbers (1, 2, 3...). But then I realized that if I ever had multiple servers or needed to merge databases, those numbers would conflict. I needed something unique across the entire system, not just within one database.
That is when I discovered UUIDs. After learning about the different versions, I started using V4 UUIDs for user IDs and V5 UUIDs for generating consistent IDs from names. This guide will teach you everything you need to know about UUIDs. What they are, the different versions, when to use each, and how to generate them.
Quick access: Use our free UUID generator here
What is a UUID? Simple Answer
A UUID (Universally Unique Identifier) is a 128-bit number used to uniquely identify information in computer systems. It is usually written as a 36-character string in this format:
Format: xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx
Example: 550e8400-e29b-41d4-a716-446655440000
Breakdown of the example:
550e8400= first 8 characters (time-low)e29b= next 4 characters (time-mid)41d4= next 4 characters (version and time-high)a716= next 4 characters (variant and clock sequence)446655440000= last 12 characters (node)
Why UUIDs are special:
- They are unique across all devices and all time
- No central authority is needed to assign them
- You can generate them offline without checking with a server
- The probability of generating the same UUID twice is astronomically low
Why Use UUIDs?
UUIDs solve a fundamental problem in computing: how to identify things uniquely without a central coordinator.
For databases:
- Primary keys that are unique across multiple databases
- Merge databases without ID conflicts
- Hide record counts from users (unlike auto-increment IDs)
- Distribute database writes across servers
For APIs:
- Unique API keys for each client
- Resource identifiers that cannot be guessed
- Idempotency keys for preventing duplicate operations
- Request tracing across microservices
For distributed systems:
- Unique message IDs in message queues
- Transaction IDs across multiple services
- Device identifiers in IoT systems
- Session IDs in load-balanced environments
For file systems:
- Unique file names to prevent collisions
- Version identifiers for assets
- Temporary file names
- Cache keys
UUID Format and Structure
A UUID is a 128-bit number, but it is usually displayed as a 36-character string.
Standard format: xxxxxxxx-xxxx-Mxxx-Nxxx-xxxxxxxxxxxx
Where:
x= hexadecimal digit (0-9, a-f)M= UUID version (1, 3, 4, or 5)N= UUID variant (usually 8, 9, a, or b)
Example with version marked:
550e8400-e29b-41d4-a716-446655440000
- The
1after the third dash indicates this is version 1
Example with version 4:
550e8400-e29b-44d4-a716-446655440000
- The
4after the third dash indicates this is version 4
UUID Variants
| Variant | Description | Most common? |
|---|---|---|
| Variant 0 | Reserved for NCS compatibility | No |
| Variant 1 | RFC 4122 (current standard) | Yes |
| Variant 2 | Reserved for Microsoft | No |
| Variant 3 | Reserved for future use | No |
Most UUIDs you encounter today are variant 1 (RFC 4122).
UUID Versions Explained in Detail
There are five main versions of UUIDs. Each has different properties and use cases.
Version 1 – Time-Based UUID
Version 1 UUIDs are generated using the current timestamp and the MAC address of the computer's network card.
How it works:
- 60 bits = timestamp (100-nanosecond intervals since 1582)
- 48 bits = MAC address of the generating device
- 14 bits = clock sequence (to avoid duplicates if time goes backward)
Example: f81d4fae-7dec-11d0-a765-00a0c91e6bf6
Pros:
- Chronologically sortable (UUIDs increase with time)
- Useful for event ordering
- No collisions if generated correctly
Cons:
- May expose the MAC address of the generating machine (privacy concern)
- Predictable (someone could guess future UUIDs)
- Requires access to MAC address (not available in some environments)
Best for:
- Event logging where order matters
- Database keys when chronological ordering is useful
- Distributed systems where time ordering is important
Version 2 – DCE Security UUID
Version 2 UUIDs are similar to V1 but include POSIX UID/GID (user/group identifiers).
How it works:
- Same as V1, but with local domain and identifier
- Incorporates user or group ID
Example: e902893a-9d22-11e1-9b23-000c29e0b9f0
Pros:
- Embeds user or group information
- Useful for security contexts
Cons:
- Rarely used in modern applications
- Limited support across programming languages
- Complex to implement
Best for:
- Legacy DCE (Distributed Computing Environment) systems
- Security-sensitive applications (rarely)
Note: Most UUID generators, including ours, do not generate V2 because it is rarely used.
Version 3 – Name-Based UUID (MD5)
Version 3 UUIDs are generated by hashing a namespace and name using MD5.
How it works:
- Choose a namespace (DNS, URL, OID, or X.500)
- Combine namespace with a name
- Hash with MD5
- Extract 128 bits and set version bits
Example:
- Namespace: DNS
example.com - Name:
my-resource - Result:
3d813cbb-47fb-32ba-91df-831e1593ac29
Standard namespaces:
| Namespace | Value | Use case |
|---|---|---|
| DNS | 6ba7b810-9dad-11d1-80b4-00c04fd430c8 |
Domain names |
| URL | 6ba7b811-9dad-11d1-80b4-00c04fd430c8 |
URLs |
| OID | 6ba7b812-9dad-11d1-80b4-00c04fd430c8 |
Object identifiers |
| X.500 | 6ba7b814-9dad-11d1-80b4-00c04fd430c8 |
X.500 distinguished names |
Pros:
- Deterministic (same input always produces same UUID)
- No randomness (can be regenerated)
- Good for deduplication
Cons:
- MD5 is considered cryptographically broken (not a problem for UUIDs)
- Not suitable for security-sensitive applications
Best for:
- Generating consistent IDs for resources
- File identification across systems
- Caching keys
- Anywhere you need the same ID for the same name
Version 4 – Random UUID
Version 4 UUIDs are generated using random numbers. This is the most commonly used version.
How it works:
- 122 bits of random data
- 6 bits for version and variant
- Essentially random
Example: 550e8400-e29b-41d4-a716-446655440000
Pros:
- Privacy-safe (no MAC address exposure)
- Unpredictable (good for security)
- Easy to generate anywhere
- No coordination needed
Cons:
- Not sortable by time
- Higher (but still astronomically low) collision probability than V1
Collision probability:
- To have a 50% chance of a collision, you need to generate 2.71 × 10¹⁸ UUIDs
- That is 2.7 quintillion UUIDs
- You could generate 1 billion UUIDs per second for 85 years and still have less than 50% chance of a collision
Best for:
- Database primary keys
- API keys and tokens
- Session identifiers
- Any general-purpose unique ID
Version 5 – Name-Based UUID (SHA-1)
Version 5 UUIDs are similar to V3 but use SHA-1 instead of MD5.
How it works:
- Same as V3, but uses SHA-1 hash
- More secure than MD5
Example:
- Namespace: DNS
example.com - Name:
my-resource - Result:
21f7f8de-8051-5b89-8680-0195ef798b6a
Pros:
- Deterministic (same input always produces same UUID)
- SHA-1 is more secure than MD5
- No randomness
Cons:
- Slightly slower than V3 (but negligible)
- SHA-1 is also considered weakened (still fine for UUIDs)
Best for:
- Same as V3, but preferred over V3
- File versioning
- Namespace-based resource identification
- Anywhere you need deterministic, reproducible UUIDs
UUID Versions Comparison Table
| Version | Name | Generation Method | Deterministic | Sortable | Privacy | Best For |
|---|---|---|---|---|---|---|
| V1 | Time-based | Timestamp + MAC | No | Yes | Low | Event logs, time-ordered data |
| V2 | DCE Security | Timestamp + UID/GID | No | Yes | Low | Legacy DCE systems |
| V3 | Name-based (MD5) | MD5 hash | Yes | No | N/A | Deterministic IDs (legacy) |
| V4 | Random | Random bits | No | No | High | General purpose, API keys, DB keys |
| V5 | Name-based (SHA1) | SHA-1 hash | Yes | No | N/A | Deterministic IDs (preferred) |
Which UUID Version Should You Use?
Here is my recommendation based on common use cases.
Use V4 (Random) for most applications:
- Database primary keys
- User IDs
- Session tokens
- API keys
- Anywhere you need a unique, unpredictable identifier
Use V1 (Time-based) when order matters:
- Event logging
- Message queue IDs where order is important
- Time-series data
- When you need to sort by creation time
Use V5 (Name-based) for deterministic IDs:
- Generating the same ID for the same resource across systems
- File identification (same file always gets same UUID)
- Caching keys
- Deduplication
Avoid V3 (use V5 instead):
- V5 is more secure than V3
- Use V3 only for compatibility with existing systems
Avoid V2:
- Rarely needed in modern applications
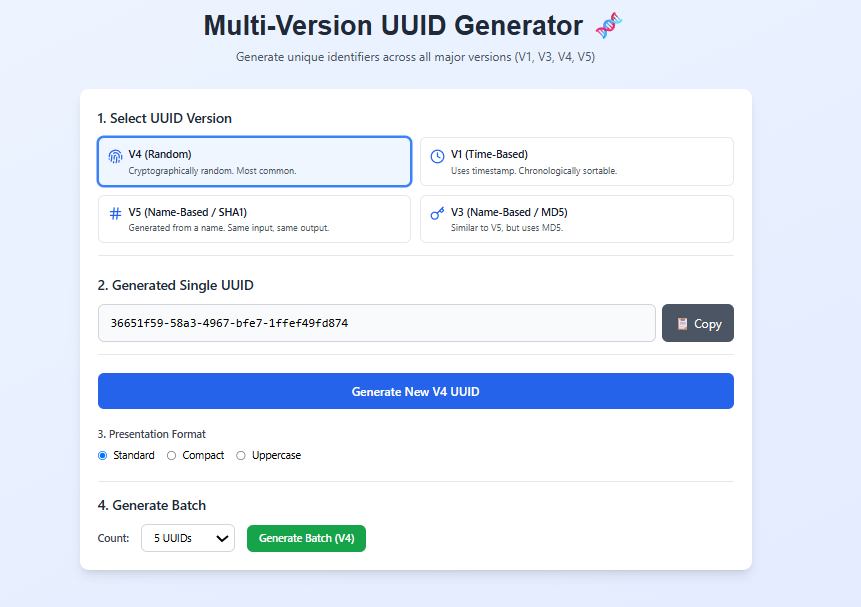
How to Use Our UUID Generator
Our UUID generator makes it easy to generate UUIDs of different versions.
Step 1: Select the UUID version:
- V1 (Time-based)
- V3 (Name-based with MD5)
- V4 (Random)
- V5 (Name-based with SHA-1)
Step 2: For V3 and V5, enter:
- Namespace (DNS, URL, OID, or X.500)
- Name (any string)
Step 3: Choose your output format:
- Standard (with dashes):
550e8400-e29b-41d4-a716-446655440000 - Compact (without dashes):
550e8400e29b41d4a716446655440000 - Uppercase:
550E8400-E29B-41D4-A716-446655440000
Step 4: For batch generation, specify how many UUIDs you need (up to 100)
Step 5: Click Generate
Step 6: Copy individual UUIDs or copy all at once
All generation happens in your browser. No data is sent to any server.
Real-World Examples of UUID Usage
Example 1: Database Primary Key
Instead of using auto-incrementing integers:
-- Traditional (can conflict when merging databases)
CREATE TABLE users (
id INT AUTO_INCREMENT PRIMARY KEY,
name VARCHAR(100)
);
-- Using UUID (unique across all databases)
CREATE TABLE users (
id CHAR(36) PRIMARY KEY,
name VARCHAR(100)
);
Example 2: API Key Generation
import uuid
# Generate a unique API key for a new user
api_key = str(uuid.uuid4())
# Result: '550e8400-e29b-41d4-a716-446655440000'
Example 3: Deterministic File ID
import uuid
# Same file always gets the same ID
file_id = uuid.uuid5(uuid.NAMESPACE_DNS, 'https://example.com/files/document.pdf')
# Result always the same for that URL
Example 4: Event Logging with V1
import uuid
# V1 UUIDs are chronologically sortable
event_id = uuid.uuid1()
# Earlier events have smaller UUIDs
UUID Format Options
Standard Format (with dashes)
Format: xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx
Example: 550e8400-e29b-41d4-a716-446655440000
When to use: Most common, required by many systems
Compact Format (without dashes)
Format: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
Example: 550e8400e29b41d4a716446655440000
When to use: URLs, file names, space-constrained storage
Uppercase Format
Format: XXXXXXXX-XXXX-XXXX-XXXX-XXXXXXXXXXXX
Example: 550E8400-E29B-41D4-A716-446655440000
When to use: Systems that expect uppercase, visual consistency
UUID vs Other Identifier Types
| Identifier | Length | Uniqueness | Sortable | Predictable | Use Case |
|---|---|---|---|---|---|
| Auto-increment integer | 4-8 bytes | Within single DB | Yes | Yes | Simple apps |
| UUID V4 | 16 bytes (36 chars) | Global | No | No | Distributed systems |
| UUID V1 | 16 bytes (36 chars) | Global | Yes | Yes (time) | Time-ordered data |
| ULID | 26 chars | Global | Yes | No | Modern alternative |
| NanoID | 21 chars | Global | No | No | Shorter alternative |
| Snowflake ID | 8 bytes | Global | Yes | Yes (time) | Twitter-style IDs |
UUID Collision Probability
One common concern is whether UUIDs can collide (two identical UUIDs generated).
For V4 (random) UUIDs:
- 122 bits of randomness
- Probability of collision after generating 1 billion UUIDs: 1 in 10¹⁵
- You would need to generate 2.7 quintillion UUIDs for a 50% chance of collision
For V1 (time-based) UUIDs:
- Properly implemented, collisions should not happen
- Uses timestamp + MAC address + clock sequence
- If time goes backward, clock sequence increments
For V3/V5 (name-based) UUIDs:
- Deterministic, so same input always gives same output
- No randomness, so collisions are by design (same name = same UUID)
Real-world perspective:
- You are more likely to be struck by lightning multiple times
- You are more likely to win the lottery multiple times
- UUID collisions are not something you need to worry about
Frequently Asked Questions
Q: What is a UUID?
A: A UUID (Universally Unique Identifier) is a 128-bit number used to uniquely identify information. It is usually displayed as a 36-character string like 550e8400-e29b-41d4-a716-446655440000.
Q: What is the best UUID generator?
A: Our UUID generator supports V1, V3, V4, and V5 UUIDs, multiple output formats, and batch generation. It is free and works offline.
Q: What is the difference between UUID V1 and V4?
A: V1 uses timestamp and MAC address (sortable but exposes MAC). V4 uses random numbers (not sortable but privacy-safe). Use V4 for most applications.
Q: What is the difference between UUID V3 and V5?
A: Both are name-based (deterministic). V3 uses MD5 hash. V5 uses SHA-1 hash. V5 is more secure and preferred.
Q: Can UUIDs collide?
A: The probability is astronomically low. For V4, you would need to generate 2.7 quintillion UUIDs for a 50% chance of collision.
Q: Are UUIDs guaranteed to be unique?
A: Not mathematically guaranteed, but practically unique. The probability of collision is so low it is considered impossible in practice.
Q: How many UUIDs can I generate?
A: As many as you want. Our tool supports batch generation of up to 100 UUIDs at once.
Q: Can I generate UUIDs offline?
A: Yes. Our tool runs entirely in your browser. No internet connection is needed after the page loads.
Q: What is the difference between standard and compact UUID format?
A: Standard format includes dashes (550e8400-e29b-41d4-a716-446655440000). Compact format removes dashes (550e8400e29b41d4a716446655440000).
Q: Should I use UUID as database primary key?
A: Yes, for distributed systems. For single-server applications, auto-increment integers are fine. UUIDs are larger (16 bytes vs 4 bytes) but offer global uniqueness.
Q: What is a namespace in UUID V3/V5?
A: A namespace is a base UUID that defines the context. Standard namespaces include DNS, URL, OID, and X.500.
Q: Can I convert UUID to integer?
A: Yes, UUID is a 128-bit integer. You can convert it, but it will be a very large number (up to 340 undecillion).
Q: Is UUID the same as GUID?
A: Yes, GUID (Globally Unique Identifier) is Microsoft's implementation of UUID. They are interchangeable.
Q: Can I generate UUID V2?
A: V2 is rarely used and not supported by most generators, including ours. Use V1 or V4 instead.
Q: Is the UUID generator free?
A: Yes. Completely free. No signup. No limits.
My Final Advice
After using UUIDs in multiple production systems, here is what I have learned.
Use V4 for almost everything. It is random, privacy-safe, and has practically zero chance of collision. Unless you have a specific reason to use another version, V4 is the right choice.
Use V1 only when you need time ordering. Event logs, message queues, and time-series data benefit from sortable UUIDs. But be aware that V1 exposes the MAC address.
Use V5 for deterministic IDs. When you need the same resource to always have the same ID across systems, name-based UUIDs are perfect. Use V5 over V3.
Use compact format for URLs and file names. Removing dashes saves characters and looks cleaner. Use standard format for database keys and API responses.
Do not worry about collisions. The probability is so low that you will never encounter a collision in practice. Focus on other aspects of your system.
Generate UUIDs client-side when possible. Browser-based generation (like our tool) means no network latency and no server load.
And finally, use a good UUID generator. Our tool supports all major versions, multiple formats, and batch generation. It is free and works anywhere.
Generate UUIDs Now – Free Tool
Have questions about using UUIDs in your application? Leave a comment below. I try to answer every one.
Tags: uuid generator, what is uuid, uuid versions explained, v1 uuid, v3 uuid, v4 uuid, v5 uuid, random uuid generator, name-based uuid, time-based uuid, uuid format, uuid example, generate uuid online, uuid for database primary key, uuid for api keys, uuid for distributed systems, uuid vs auto-increment, uuid collision probability, uuid generator free online, batch uuid generator, uuid without dashes, compact uuid, uppercase uuid, uuid namespace, uuid dns namespace, uuid url namespace, uuid oid namespace, uuid x500 namespace, md5 uuid, sha1 uuid, uuid for developers, unique identifier generator